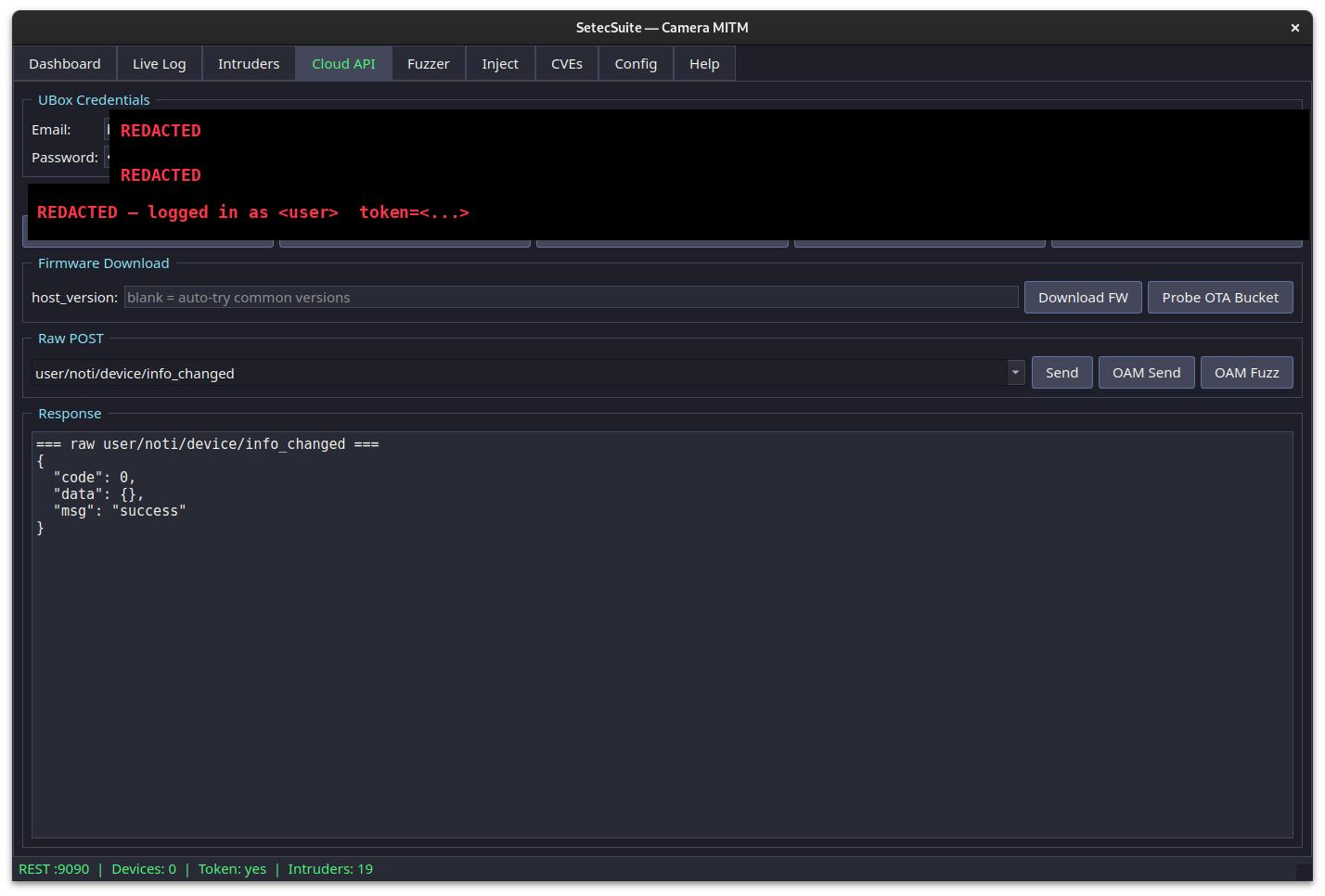
I bought a generic Chinese IP camera off a marketplace listing — the kind that costs less than dinner. Plugged it in, watched what it does, then started taking it apart. Three weeks later I had extracted hardcoded admin secrets, forged authenticated requests against the vendor's operator API, mapped the entire cloud backend, identified eight leaked Google & Alibaba API keys, confirmed three CVEs apply to the device, and put together this report.
The vendor is UBIA Technologies — legal name Shenzhen Qingshi Internet Technology Co., Ltd. (深圳市青视互联科技有限公司), founded 2014, based in Bao'an District, Shenzhen. They claim to have shipped over three million low-power cameras. The hardware is the same Ingenic T31 reference design sold under at least nine brand names — UBox, UCon, YBox, Javiscam, Funstorm, i-Cam+, Soliom+, icamplus, Jarvis-, xega — all the same firmware, all the same backend, all the same problems.
UBIA didn't respond when CISA tried to contact them about the existing CVE-2025-12636. They probably won't respond to this either. I'm publishing under a 90-day responsible-disclosure window from April 2026 with sensitive specifics redacted; CISA coordinators and UBIA security contacts can request the unredacted artifact pack at the email below.
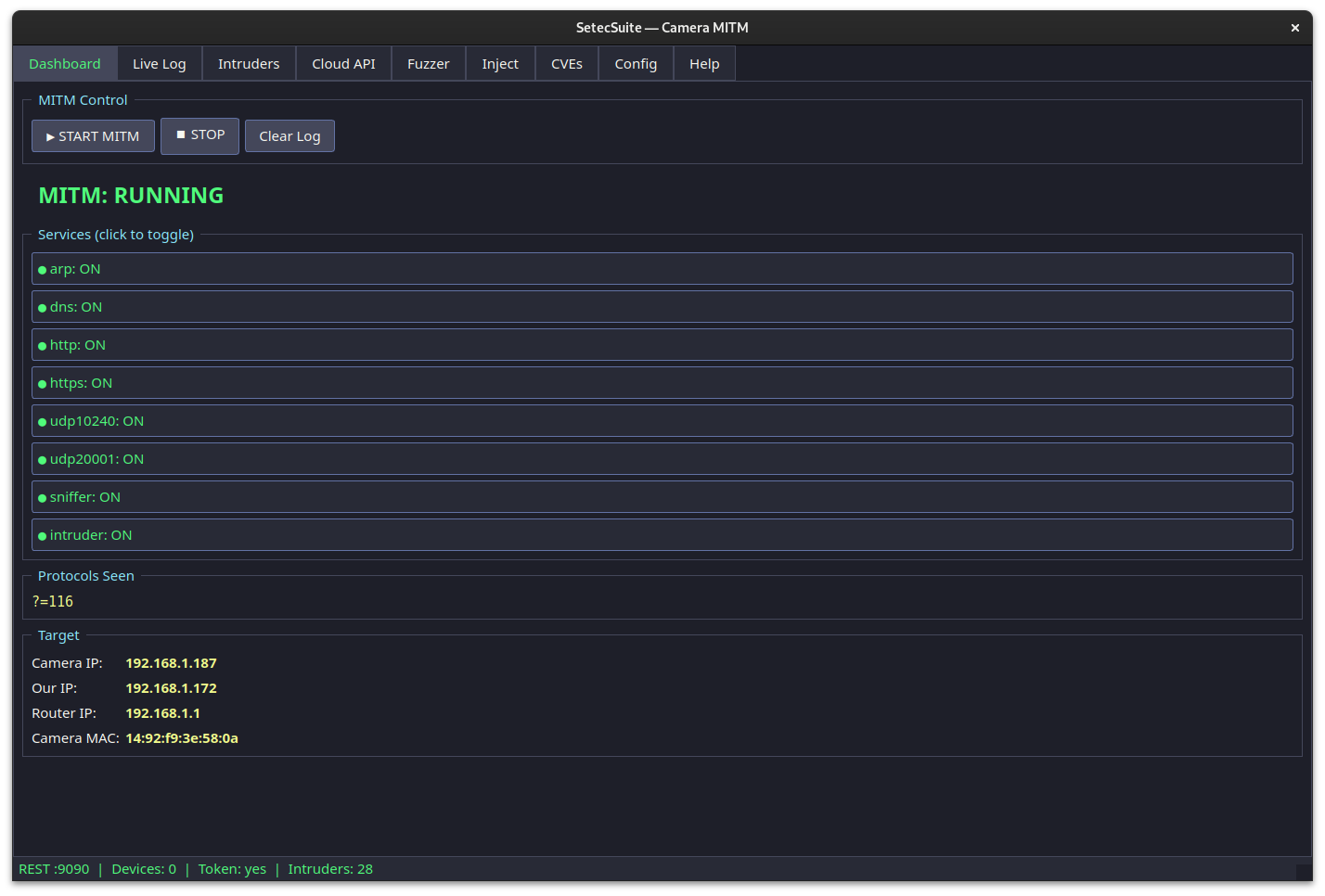
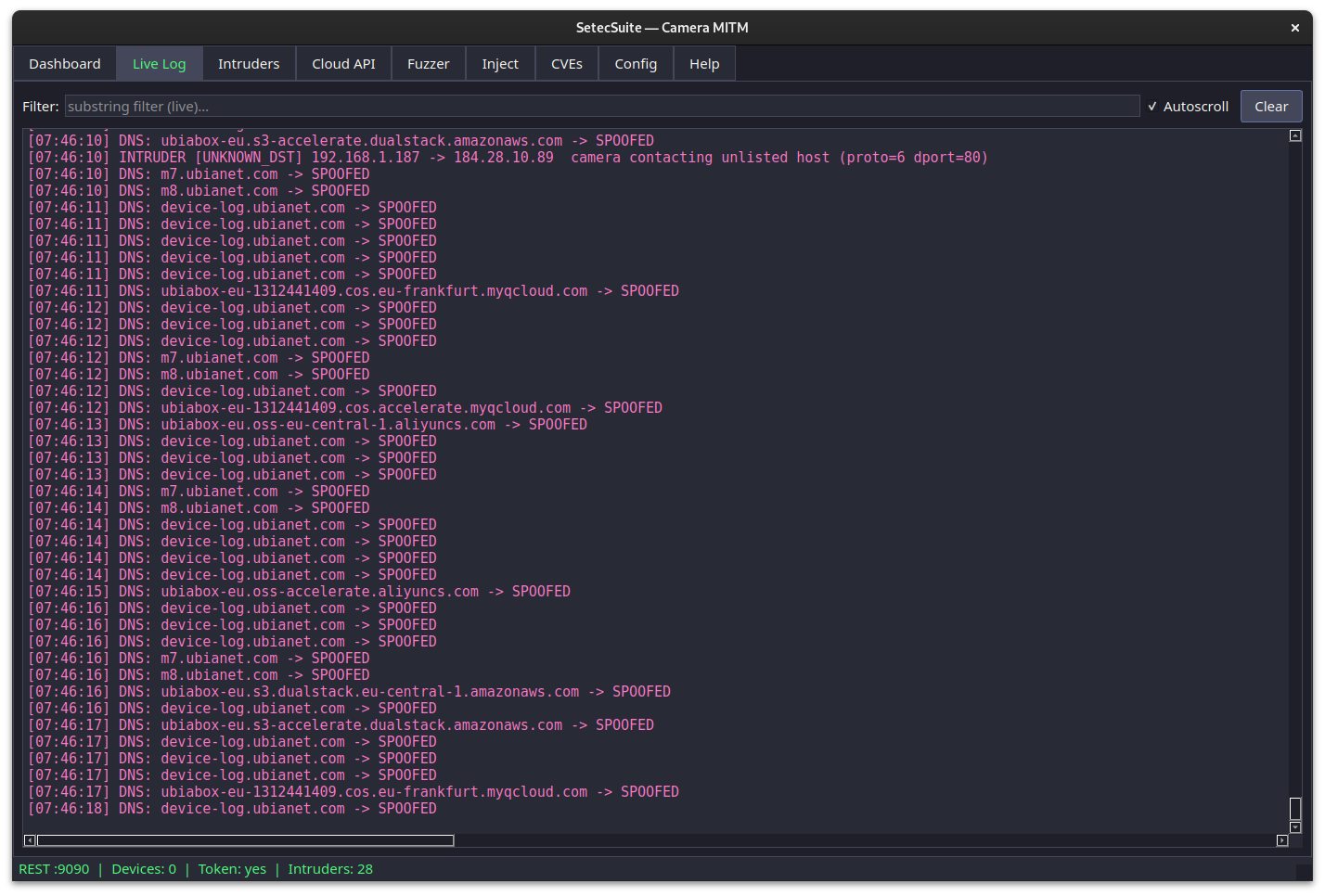
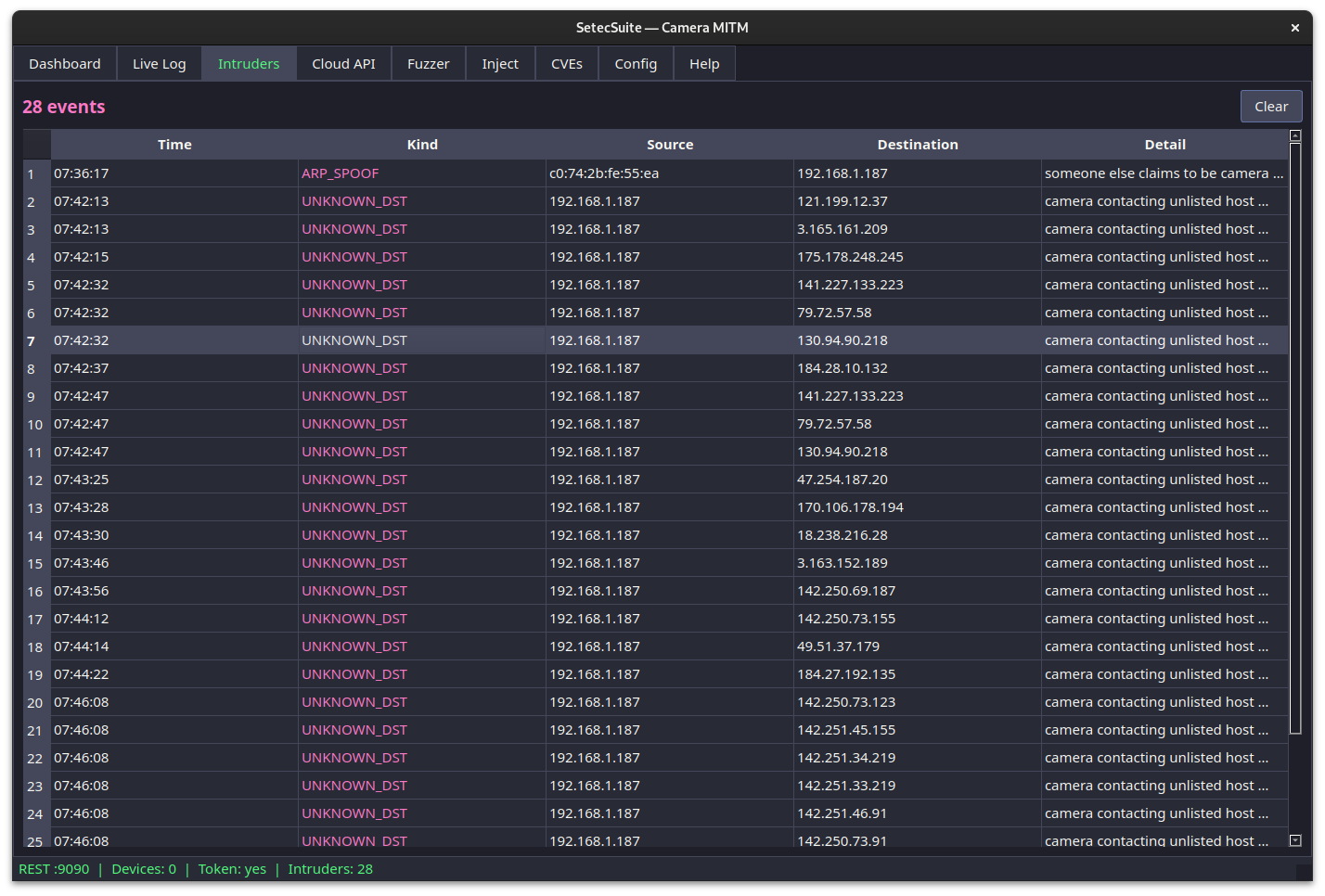
This report covers 20 distinct findings, 3 applicable CVEs, the full toolchain we built, and the failed paths we tried so other researchers don't have to repeat them. Everything below is from research on a device I own. No production user data was touched. PII has been redacted from all example payloads. The source code for every tool is published at repo.seteclabs.io/SetecLabs/cam-mitm.
Methodology: passive observation first, MITM on a controlled LAN, decompilation of the official Android app, native binary analysis of the bundled libUBICAPIs.so series, original PoC verifiers built from scratch (no public exploit code reused), and direct reproduction against my own camera. No port scans were run against the vendor's infrastructure. No credentials beyond my own account were used. No production accounts were touched.